Free-riding Attack
NOTICE: This attack is applicable to ISPs that do not account for TCP retransmission. As of August 2017, all Korean cellular ISPs are still vulnerable to this attack.
The "free-riding" attack avoids accounting of the cellular traffic by tunneling the actual payload in a fake TCP header that masquerades as retransmission.
Figure 1. Free-riding attack process (uplink case)
ATTACK SETUP
- It requires a collaborating TCP tunneling proxy that relays the tunneled packets and real traffic between the client and the server.
ATTACK DESIGN
-
Client:
Client runs a modified VTun daemon (vtund) that captures all
the packets from applications and insert new TCP/IP headers
destined to the tunneling proxy. On initialization, vtund
creates a TCP connection to the proxy and multiplexes all
TCP packets over the client-to-proxy connection. We allow the
client to configure the retransmission factor, which is the
number of retransmission packets it would send per packet on
average.
-
Proxy:
The tunneling proxy detunnels the packets from the
client/server and relays the original packets to the real
destination. After extracting the original packet, the proxy
forwards it to a NAT table. NAT is responsible for
translating the client/server-side IP address and the port
number to those of the proxy and vice versa.
- Optimizations: To evade the tunnel header detection by the accounting system, vtund encrypts the payload of all tunneled packets using RC4. Optionally, it applies packet compression using the LZO algorithm.
Performance of Tunneled Traffic
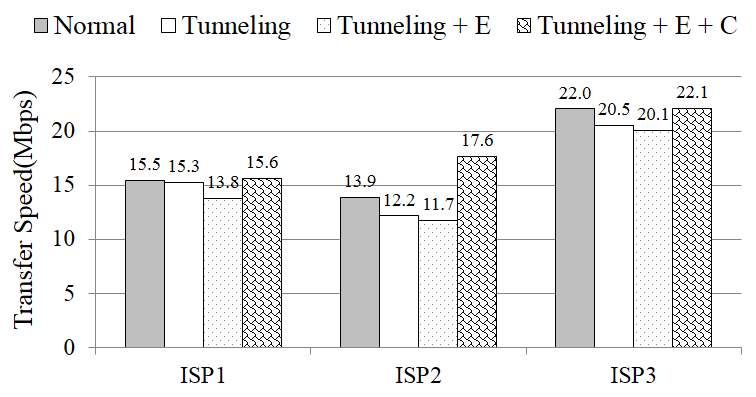
Figure 3. Comparison of download throughputs with SpeedTest.
Normal=innocent usage, Tunneling="free-riding" attack,
E=encryption, C=compression
Normal=innocent usage, Tunneling="free-riding" attack,
E=encryption, C=compression
TEST SETUP
- We measure the effective bandwidth as we use the tunneling proxy. We use the SpeedTest app to measure the download throughputs from a server located in Seoul, South Korea. We run the tests for five times and show the average numbers.
RESULTS
- We see that the download throughputs with tunneling are between 15.6 to 22.1 Mbps when we apply both encryption and compression. These are almost similar to those without tunneling, which implies that the tunneling overhead can be hidden by compression.
- The tunneling throughputs without compression show 11.7 to 20.1 Mbps, which is 9% to 16% lower than the normal throughputs due to tunneling and encryption overheads. But the throughputs look high enough to be used in practice.
Demo Video
Source Code
- Source code (proxy + client-side code) will be released when Korean ISPs fix their accounting systems.
Publications
- Gaining Control of Cellular Traffic Accounting by Spurious TCP Retransmission
Younghwan Go, Jongil Won, Denis Foo Kune, EunYoung Jeong, Yongdae Kim, and KyoungSoo Park
In Proceedings of the 21st Annual Network and Distributed System Security Symposium (NDSS 2014)
San Diego, CA, USA, February 2014 - Impact of Malicious TCP Retransmission on Cellular Traffic Accounting
Younghwan Go, Denis Foo Kune, Shinae Woo, KyoungSoo Park, and Yongdae Kim
In Proceedings of the 5th Annual Wireless of the Students, by the Students, for the Students Workshop (S3 2013)
Miami, FL, USA, September 2013 - Awarded Best Paper - Towards Accurate Accounting of Cellular Data for TCP Retransmission
Younghwan Go, Denis Foo Kune, Shinae Woo, KyoungSoo Park, and Yongdae Kim
In Proceedings of the 14th International Workshop on Mobile Computing Systems and Applications (HotMobile 2013)
Jekyll Island, GA, USA, February 2013
People
Students:
Younghwan Go,
Jongil Won,
Denis Foo Kune, and
EunYoung Jeong
Faculty:
KyoungSoo Park and
Yongdae Kim